TECHNICAL
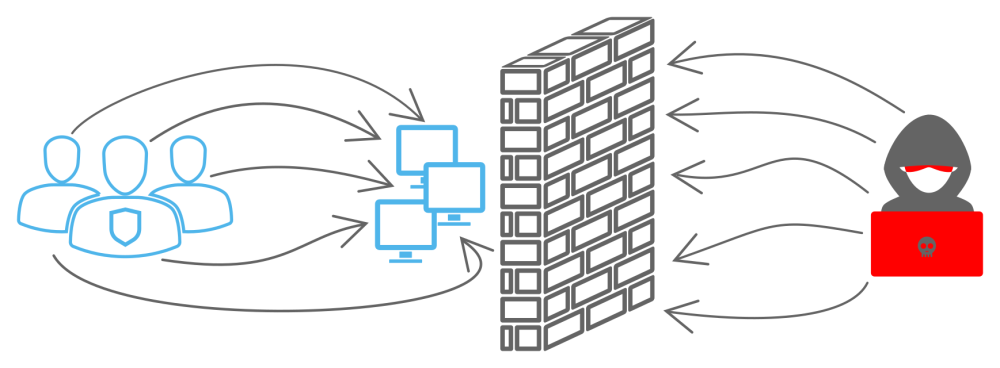
This type of exercise is designed for technical experts, e.g. system administrators. Exercise participants train on a designated infrastructure that they secure and defend against simulated enemy attacks thus training and preparing for a real crisis situation.
Cyber Czech
Cyber Czech is a national technical exercise aimed to practice the practical skills in defending the assigned network against cyber attacks.
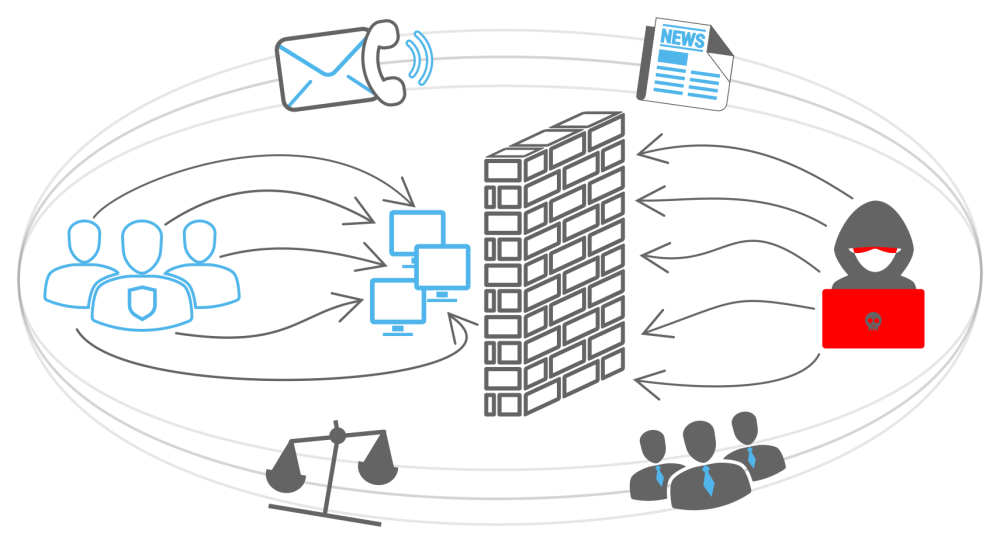
The exercise is based on a prepared scenario that reflects real cyber threats and puts them in a fictitious geopolitical context. During the exercise, two teams face each other – the Blue Team (team of participants) and the Red Team (team of attackers). Blue Teams are responsible for the administration of the information systems, ensuring their security and handling cyber security incidents that can happen in elements of critical information infrastructure, operators of essential services and important information systems. Their task is also to communicate with regular users, the media and the governmental CERT team (GovCERT.CZ).The attacking Red Team simulates activities of hackers who in real time use various types of attacks aimed at infrastructure of Blue Teams.
Until now the Cyber Czech exercise was developed in collaboration with experts from Masaryk University in Brno and was executed at their specially modified infrastructure of the Cybernetic Proving Range KYPO. 
>>> Video from Cyber Czech 2016
>>> Gallery - Cyber Czech
Crossed Swords
Crossed Swords is a technical cyber exercise that focuses on training penetration testers, digital forensic professionals, and situational awareness. It aims to advance their skills in preventing, detecting and responding to full-scale cyber operations. Many of the exercise participants are then part of the Locked Shields’ Red Team. The exercise is organized by NATO CCDCOE¬* (NATO Cooperative Cyber Defence Centre of Excellence) and representatives of GovCERT.CZ participate every year.
TABLE-TOP
Table-top exercise is a non-technical type of exercise that can take many forms. One of the most common forms is that the participants sit at a table and go through the presented crisis scenario and discuss it in unthreatening environment. It is a valuable exercise for wide range of audiences, from technical experts to middle and senior management.
Objectives of table-top exercise
![]() Educating civil servants on senior positions, whose agenda is also cyber security or is directly affected by this matter. The exercise simulates crisis scenarios and situations. During execution it is possible to observe approaches of different target groups, across sectors, states and continents. Final findings have a positive impact on increasing cyber security in the Czech Republic..
Educating civil servants on senior positions, whose agenda is also cyber security or is directly affected by this matter. The exercise simulates crisis scenarios and situations. During execution it is possible to observe approaches of different target groups, across sectors, states and continents. Final findings have a positive impact on increasing cyber security in the Czech Republic..
![]() Educating students and professionals to gain a unique experience in cyber security. The exercise helps the target audience to understand the issue and increase the overall interest in cyber security.
Educating students and professionals to gain a unique experience in cyber security. The exercise helps the target audience to understand the issue and increase the overall interest in cyber security.
![]() Raising awareness of civil servants about current trends and approaches in cyber security in the Czech Republic and abroad.
Raising awareness of civil servants about current trends and approaches in cyber security in the Czech Republic and abroad.
![]() Sharing the acquired know-how with our foreign partners. The Czech Republic pursues to maintain its leading position among other states regarding the quality and experience with non-technical exercises. Reciprocally, this product is offered to close foreign partners.
Sharing the acquired know-how with our foreign partners. The Czech Republic pursues to maintain its leading position among other states regarding the quality and experience with non-technical exercises. Reciprocally, this product is offered to close foreign partners.
>>> Gallery - Electro Czech 2019
PROCEDURAL
This type of exercise aims to exercise specific processes in the field of cyber security, e.g. the organization’s reaction to a cyber attack. To keep the exercise as authentic as possible, training audience exercises from its day-to-day work environment using realistic communication channels. Emphasis is put especially on the decision making processes, internal procedures and communication. It is a complex activity demanding a lot of effort for the planning as well as the execution.
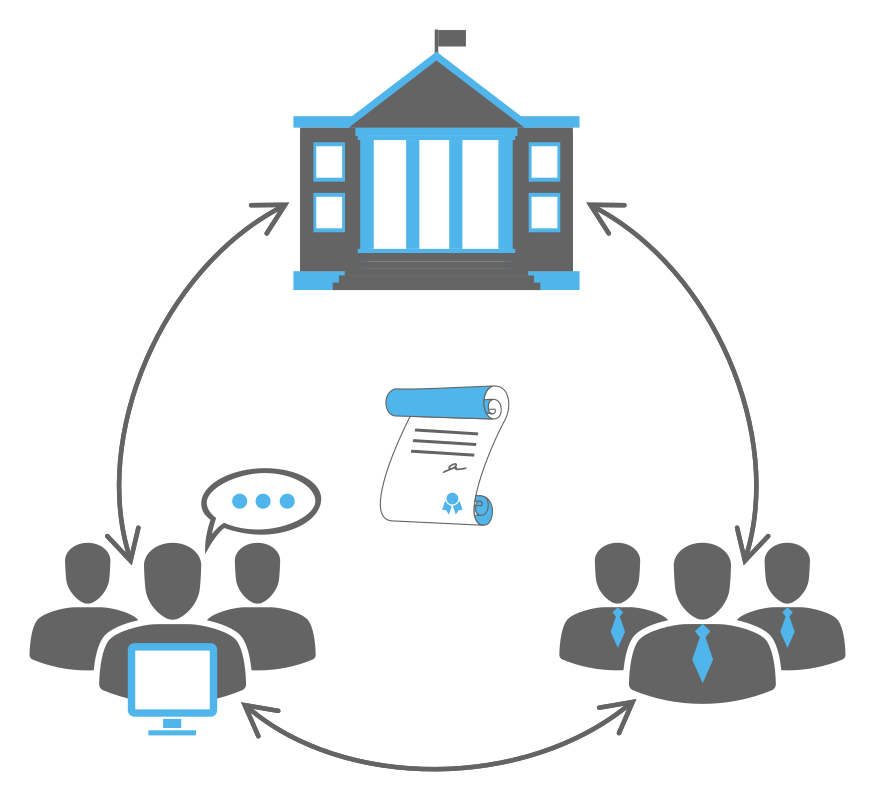
Cyber Coalition
Cyber Coalition is an exercise organized by the NATO along with the NATO CCD COE. It is one of the largest and most important exercises of its kind. Several hundred experts from member and partner countries, including European Union institutions, academic and private sector experts are involved in the exercise. The main goal of the exercise is to practice collaboration and coordination in dealing with cyber security incidents across states and sectors.
It aims to prepare participants via realistic scenario based training in order to: enhance coordination and cooperation between NATO and participating nations, strengthen nations’ ability to protect Alliance cyber space and conduct military operations in the cyber domain, and test NATO and national procedures on information sharing, situational awareness in cyber space and decision making.

The prepared scenario tasks participants to solve issues with the emphasis on the procedural and coordination aspect of the collaboration. An integral part of the exercise are cyber attacks reflecting current security trends and the legal aspects of dealing with incidents.
>>> Video from Cyber Coalition 2019
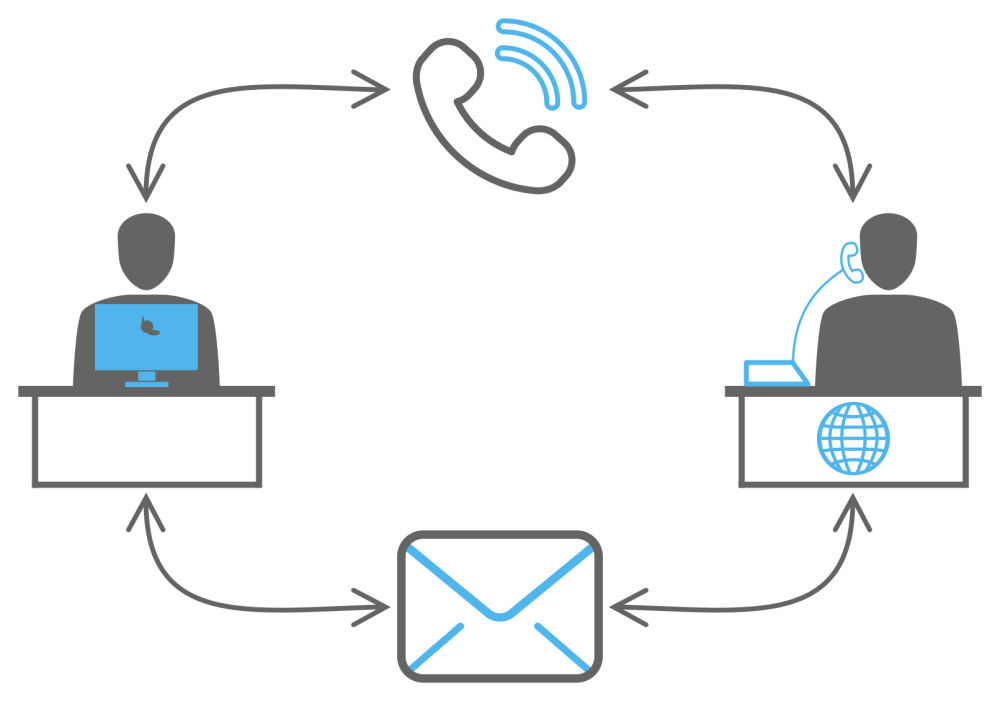
COMMUNICATION
The communication exercise aims to verify the availability of communication channels in the case of a cyber crisis. Safe, efficient and fast communication between the various actors of both the state and the private sector is crucial during crisis.
The Comm Czech exercise, which is regularly executed by NCISA, is focused on legal and natural persons obliged by Act No 181/2014 Coll., On Cyber Security.
HYBRID
Hybrid exercise focuses on all levels usually affected by the crisis (technical, decision-making/strategic, legal, media). Participants thus come from different levels with respective skills. Such an exercise covers the issue of cyber security in its entirety and simulates the real crisis situation most authentically.
Locked Shields
Locked Shields hybrid exercise organized by NATO CCD COE is a simulation of the Red Team attacks on systems and networks of Blue Teams (national) of experts protecting IT systems in the everyday real world. The exercise scenario has a realistic background. Each year the Teams are under great pressure to protect their fictitious country, created for the purpose of the exercise. Besides the technical part, a so called strategic play takes place at the same time. Its aim is to practice decision-making processes during a crisis, which takes place mainly in cyberspace and to draw attention to the differences between the technical solution of the incident and the strategic decision-making during its escalation. The exercise also includes a legal and media level.
The Czech Republic is represented in the Blue Team (competing), the White Team (organizational), Green Team (responsible for infrastructure) and in the Red Team (attackers). The Czech team consists of NCISA employees and representatives of other state entities, private and academic security communities.
Along with execution, NCISA also participates in the preparation and planning of the exercise. Planning, as well as the exercise itself, represents a unique experience for NCISA employees, which is reflected in the preparation of exercises at the national level. 
>>> Video from Locked Shields 2018
>>> Gallery - Locked Shields
National Team Results: